The Google Cloud IAM resource hierarchy provides considerable flexibility for grouping and segmenting multiple levels of resources. But with large organizations or environments that change frequently, it can be cumbersome to use.
To help make your permission settings more manageable, add conditions to role bindings - this means binding a user or group to a role only if certain conditions are met at the time of access. Let's look at some examples to illustrate. You might, for example, allow or deny access based on:
- Time of day
- Day of the week
- The type of resource attempting the access
- Resource name
- etc.
These conditions are specific to the binding of a policy. You can use GCP's Resource Manager to create and edit conditions for each policy. GCP provides forms in the Condition Builder, or you can use the Condition Editor, a free-form editor that uses Google's Common Expression Language (CEL). CEL gives you more flexibility and access to more advanced expressions and functions, but it takes time to familiarize yourself with the language. It has C-like syntax common to C++, Go, and Java.
{
"bindings": [
{
"condition": {
"expression": "request.time.getHours(\"America/Chicago\") <= 18", "title": "Daytime Access" },
"members": [
"group:gcp-devops-members@example.com"
],
"role": "roles/cloudfunctions.developer"
},
],
"version": 3
}
Not all GCP services support conditional policy bindings. Some provide different conditions than others, so it's good practice to check the documentation for each service to be aware of what is available.
Resource Tags
Another way to simplify access control is to use resource tags. A tag is a key-value pair that you attach to an organization, folder, or project.
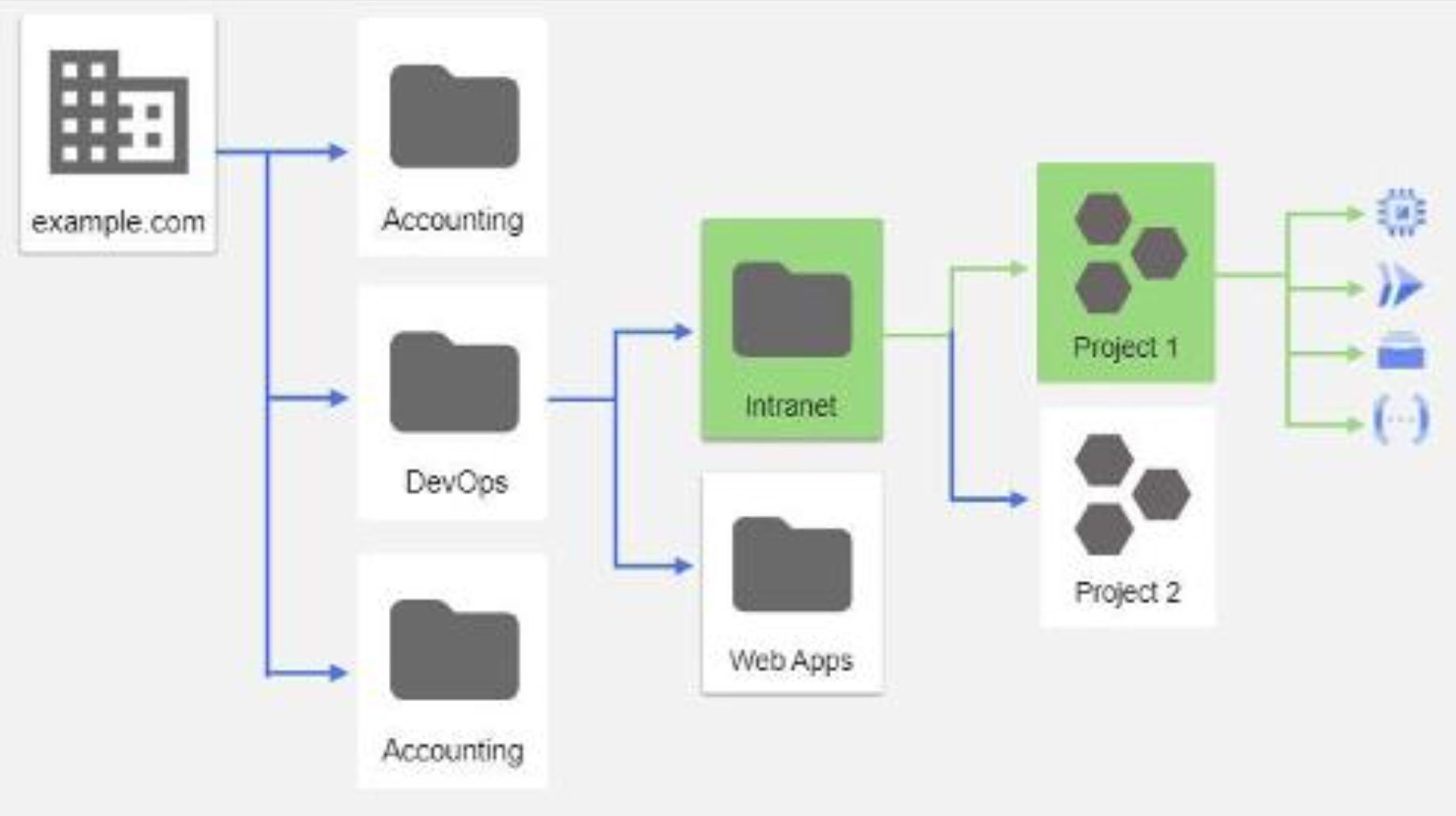
These tags are attributes you assign to roles, jobs, departments, location, types of workload, special cross-teams, or whatever other attributes make sense for your organization. Resource tags are helpful to manage granular permissions and are a good strategy for enforcing the principle of least privilege.
Once you set a tag on a resource, you can create a conditional policy to allow or deny access based on that tag. Resources always inherit tags from parent resources, so, like permissions, they require careful planning. You can always override a parent tag value by setting a new value for a tag in a child resource.
Besides policies attached to the resource, there are also other ways to set account restrictions or enforce security boundaries:
- Identity-Aware Proxy – a service that helps control access to both cloud and on-premises web applications and access controls for cloud resources and virtual machines.
- Firewalls – allow you to set restrictions to cloud resources based on traffic properties.
- Cloud Storage Permissions – in addition to the regular resource permissions, you can set fine-grained permissions.
- Access control lists on individual storage buckets.
- VPC service controls – a managed network service that helps ensure users can only access sensitive data from authorized networks and allows you to restrict resource access to allowed IP addresses, identities, and trusted client devices.
- BeyondCorp – an advanced enterprise solution that adds identity and context-aware access control, advanced threat protection, single sign-on, and other features. It's Google's implementation of the zero trust model.
Security on GCP can get complex, and sometimes there are multiple ways to manage access. However, it is essential to understand the security mechanisms for each specific service you want to implement.
About Ed Adams, CEO
Ed Adams is a software quality and security expert with over 20 years of experience in the field. He served as a member of the Security Innovation Board of Directors since 2002 and as CEO since 2003. Ed has held senior management positions at Rational Software, Lionbridge, Ipswitch, and MathSoft. He was also an engineer for the US Army and Foster-Miller earlier in his career.
Ed is a Ponemon Institute Research Fellow, Privacy by Design Ambassador by the Information & Privacy Commissioner of Canada, Forbes Technology Council Member, and recipient of multiple SC Magazine’s Reboot Leadership Awards. He sits on the board of Cyversity, a non-profit committed to advancing minorities in the field of cyber security, and is a BoSTEM Advisory Committee member.


