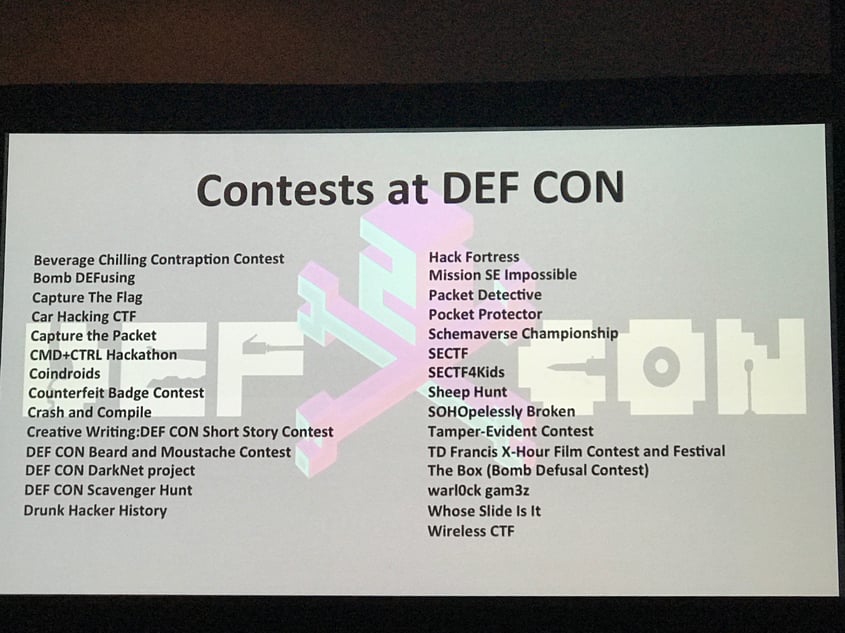
For a quarter of a century now, thousands have gathered each year at the end of July in Las Vegas for one of the world’s largest hacker conventions – DEF CON. This year, DEF CON attracted a record-breaking 25,000 attendees. If you’re a computer security professional, IT professional, journalist, federal government employee (FBI, DoD), security researcher, or a hacker with an interest in software, computer architecture, phone phreaking, hardware modification, or anything else that can be hacked, then you know DEF CON is the place to be. Attendees come from all over the world to listen to talks about the latest threats and trends, but the real draw are the various contests for everything from who can most effectively cool a beer in the Nevada heat to capture-the-flag (CTF) style competitions.
Think Like a Hacker: Practicing Real-life Scenarios with CMD+CTRL
Can you view your application from the eyes of a malicious attacker? To prevent attacks on your code, you need to understand what the hacker sees. Secure coding is not for the novice, but you can test your skills at one of the many CTF-style contests that take place at DEF CON. Security Innovation was again honored to run our CMD+CTRL Hackathon, this year in junction with Women in Security and Privacy (WISP). The two-day event started on Friday at 10AM and ended on Saturday at 6PM.
CMD+CTRL is an immersive, gamified learning experience where teams compete to find vulnerabilities in commercial-grade applications or defend an IT infrastructure in real-time. Participants immediately become immersed in a real-world environment where they learn attack and defense is about thinking on your feet combined with some creativity and adaptability. Security Innovation has a variety of real-like web applications, but for DEF CON, we used two: Gold Standard (an advanced banking website) and Shred (an eCommerce Skateboard Shop).
Given the media has reported more and more widespread malicious attacks, it’s no surprise that the number of teams that entered the CMD+CTRL contest was up by 450% since last year, with over 450 people playing.
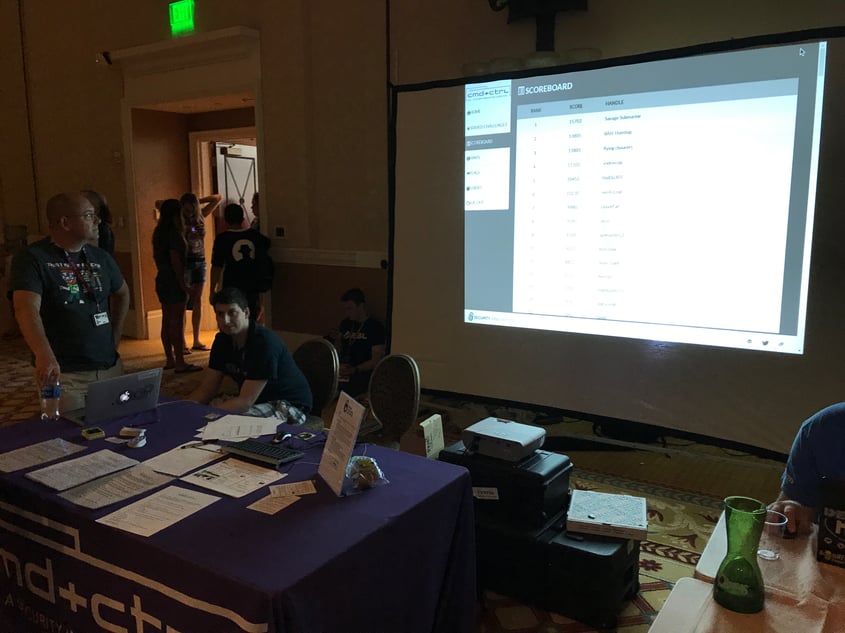
Dominating the Leaderboard
There’s nothing like a sweaty room full of wannabe hackers. Seriously. The 40-participant seating in our contest area was full throughout the event. Participants played from anywhere they could: the hallway floor, their hotel room, even the bathroom down the hall. It all got down and dirty.
The scoring system is a bit like a standardized test that you may have taken to get into college. Each challenge has a point value based on complexity, with challenges ranging from common vulnerabilities such as SQL Injection (SQLi) to advanced cryptanalysis and cipher cracking tests. 235 teams played, with almost half scoring more than 500 points.
Game Over: Lessons Learned
After two crazy, but fun days, several teams emerged victorious. In first place was BAH-Humbug; second place winners were Savage Submarines and third place the Flying Chaucers. All in all, participating teams got a chance to utilize techniques in a real-world setting, receiving real-time and post-game feedback.
It was great seeing how into the contest all of the players were. Everyone was heads down and hacking away for hours. Tons of vulnerabilities were scored, and we had a number of non-intentional vulnerabilities pointed out as well.
Immersive learning like CMD+CTRL is a good way to learn what you do (or don’t) know about software security. It is fun, stimulates the senses, adds a gaming aspect, gives users the right to “safely” fail and learn by doing. This type of learning has a 100% attention rate from users, is 5 times more engaging than any other media, and yields a 75 – 90% knowledge retention rate. 1
It is no wonder the immersive, gamified learning is becoming a popular way to train development teams.
Visit our website to learn more about our CMD+CTRL and how your team can outsmart, outlast and defend your organization from malicious attackers.
1Touchstone Research: https://touchstoneresearch.com/infographic-immersive-learning-in-corporate-training/